Real-Time Reporting and Analytics for JDE and Oracle EBS
"*" indicates required fields

See for yourself why over 500K+ users are using insightsoftware
Out-of-the-Box ERP Reporting Tools Take Valuable Time Away from Your Finance Team
Your Month-End Close Process Takes Days or Weeks to Complete
Identifying and fixing reconciliation issues becomes a manual effort and slows down your closing process when your ERP solution can’t drill down from summary to detail. You’re spending more time consolidating data than you are on regular financial processes.
You’re Making Strategic Business Decisions Without Accurate Information
Manually exporting data from JDE and Oracle EBS into Excel to create reports and analyze data is not just inefficient, it’s also prone to errors. If you aren’t confident in your numbers, the executive team responsible for critical business decisions won’t be either.
You Don’t Have the Technical Skills to Build Your Own Reports or Dashboards
Out-of-the-box reporting tools provided with JDE and Oracle EBS tend to require heavy IT involvement to manage. Waiting on IT causes serious delays for your finance team when it comes to modifying recurring reports and creating ad hoc requests.
Speed Up Day-to-Day Finance Processes with a Powerful, Easy-to-Use Reporting Solution for JDE and Oracle EBS
Close Your Books Faster
Shrink your month-end and year-end close processes by up to 50% with an all-in-one reporting and analytics tool for JDE and Oracle EBS. With real-time reporting, automated report distribution, and drill-down into transactions, you can free up time and maximize your investment.
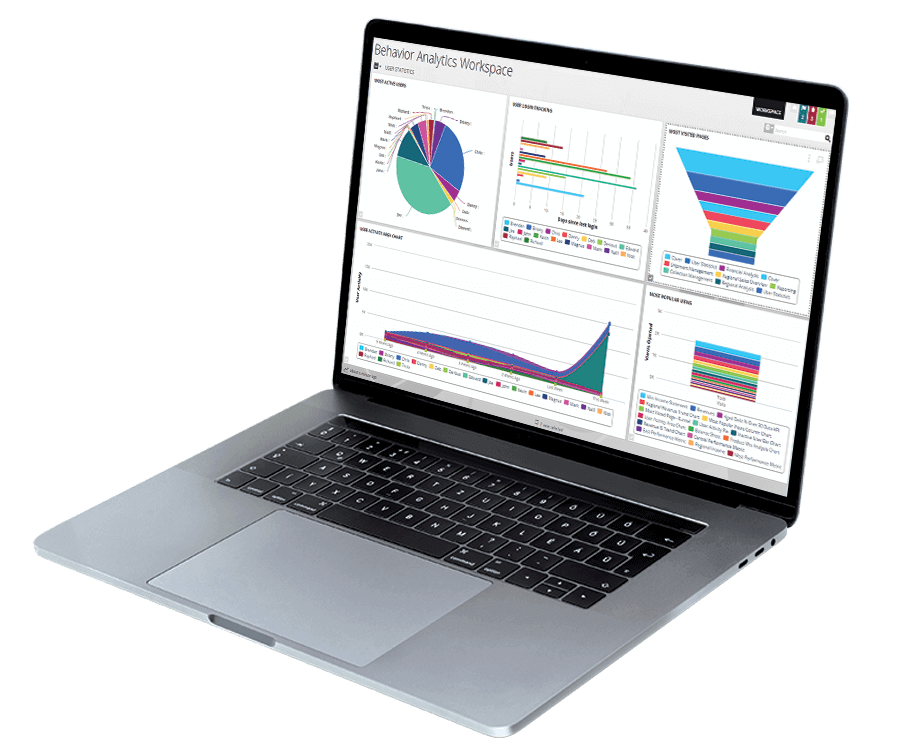
Deliver Immediate Value From Your Data
After a fast and easy install, Hubble provides a flexible library of 240 pre-built, out-of-the-box report templates that are easy to build and customize. Your finance team can start creating accurate reports and making decisions right away without requiring technical expertise.

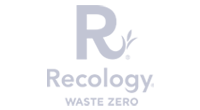
Track Key Metrics
Bring all your key metrics into focus with easy-to-consume, real-time web dashboards, and analytics. With Hubble’s data visualization, users across your organization can monitor KPIs, analyze trends, collaborate through discussions, and drill into underlying ERP transactions.
Introduce a Governed Reporting Process
Reduce risk and help with compliance in regulated industries or where required by auditors. A host of controls—including full integration with EBS and JDE security, read-only data in reports, workflows and approvals, and different user types—governs access to functionality and provides a full audit trail.
Integrates with:

How to Compare Reporting & BI Solutions
Reporting and Business Intelligence (BI) solutions begin and end with data—not just how the data are collected, but also how they are stored, organized, and accessed. With a saturated market full of solutions to choose from, you need to have a clear understanding of your data needs before you start comparing your options.
In this white paper, you will learn:
- What to look for in reporting and/or BI software.
- Why a reporting and BI solution is essential for growth
- How to avoid reporting and BI solution implementation failure
To assist with your software selection process and help you find a solution that fits your current ERP system and IT infrastructure, we have also created a framework for evaluating third party solutions.
You need to have a clear understanding of your data needs before you start comparing your options.
Work with the #1 Financial Reporting Vendor for ERPs and EPMs

"I have never seen anything quite like Hubble, and as a project manager, I think that Hubble should be part of your tool kit.”
Request an Estimate